Why manual security logbooks fail audits
Manual logbooks were designed for a time when operational verification was mostly visual and local. Today, audit requirements demand consistency, traceability, and verifiable time and location records across multiple sites. Unfortunately, paper-based logs struggle to meet those standards.
Common logbook issues
Backfilled entries, missing times, illegible handwriting, inconsistent formats, and lack of evidence.
Audit impact
Auditors cannot validate patrols or incidents reliably, resulting in non-conformances and corrective actions.
Typical failure points auditors highlight
- No proof of presence: Signatures alone do not confirm guards were on-site.
- Inconsistent entries: Different writing styles and formats across shifts.
- Late or retrospective filling: Entries may be completed hours later.
- No traceability: Difficult to link incidents, patrols, and responses in one timeline.
- Storage & retrieval risk: Books go missing, pages tear, or become unreadable.
What auditors expect today
Many audit frameworks emphasize evidence-based controls. Whether your audits are internal, customer-driven, or tied to certification standards, the expectations are increasingly similar:
- Time-stamps that cannot be easily manipulated
- Evidence (photos, acknowledgements, digital signatures where needed)
- Standardized reporting across all sites and shifts
- Supervisor visibility and review capability
- Secure storage and controlled access to records
How digital systems fix the gaps
Digital security management systems replace manual entries with structured workflows and verifiable logs. Instead of relying on handwritten records, data is captured at the time of action—creating a clearer, more reliable operational history.
Digital log advantages
Automatic timestamps, structured forms, evidence capture, and consistent reporting formats.
Management advantages
Central dashboards, alerts, easier investigations, and faster audit preparation.
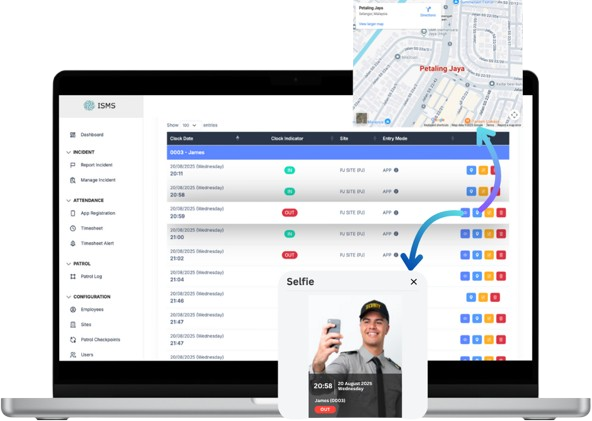
How ISMS supports audit readiness
ISMS by ENTRYIQ Technologies is designed to modernize on-site security operations while improving audit readiness. It provides structured, traceable records for daily activities and helps supervisors maintain operational visibility.
- Guard attendance tracking with location-based verification
- Patrol monitoring with structured reporting
- Geo-fencing to reduce off-site attendance records
- Central reporting for faster audit reviews and compliance checks
Practical rollout steps
The safest approach is to start with one site, standardize the workflow, and then expand. This allows your team to validate configurations and ensure adoption without disrupting operations.
- Start with a pilot site and define reporting templates
- Enable location-based clock in/out and supervisor review
- Train guards on consistent reporting
- Review logs weekly and adjust workflow rules
- Roll out site-by-site to standardize compliance